There is a reason many people loathe Microsoft software. Before you consider flaming me for that statement, I realize all software has flaws, bugs and eventually crashes. In my experience, even if it’s patched and up to date, the following image happens FAR too frequently with Microsoft software.
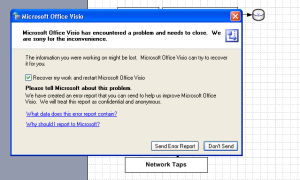
I don’t recall having the same issues with Concept Draw, even with complex diagrams. Since I’m just tired of having to redo work over again, good-bye Visio, I’ve just purchased your replacement.
Tag Archives: windows
How to secure your home PC
Whether you have a Mac or a Windows PC, there are some basic steps you can take to reduce the risk and personal impact of a malware infection. This advise is especially impactful when you have just purchased a new Mac or Windows system. There are several steps that you can take to protect your new investment and more importantly your information. In the following detail, I mainly focus on Windows as that’s the main technology that my non-IT type friends ask about.
Basically what you should be doing is:
- Ensure that a hardware firewall/router is in between the internet and the PC (I’ll just call it a firewall from now on)
- Use a recognized brand name like Linksys, avoid the no-name generics as they often have bad defaults and don’t implement the stateful-packet-inspection that you want to filter out most of the cruft on the Internet from reaching your PC
- Ensure all default passwords on the firewall and PC have been changed
- When you initially turn on the power to your PC and to your firewall, do NOT have them connected to your cable or DSL modem initially. Do the setup of your firewall and PC first in order to ensure malware doesn’t have a chance to get at your shiny new PC before you’ve turned on the needed protection
- Point a browser to your firewall (likely 192.168.0.1 or 192.168.1.1) and change the default administrator password. This is very important, as some malware will seek out your firewall and try to use the manufacturer default password to change things like your DNS server settings – inserting the bad guys in between you and the rest of the Internet (eg. forcing your traffic to them first before it goes to your bank)
- All normal accounts used for day-to-day business on the computer should NOT have administrator privilege (see my post on running without admin privileges)
- On Windows XP, Vista (and I think 7), the default “user” that accesses the PC has full administrative privilege, that enables software installation and configuration changes. This is very dangerous, as malware that you come in contact with from infected emails or websites use this privilege to install their spyware, keyloggers, backdoors and other nasty stuff on your PC – without your explicit permission
- Set a password for your Administrator account
- Create a new user right away, before you setup your email, music, photos, documents, etc; ensure that new user is NOT a Computer Administrator
- Always login with this non-Administrator username for your day-to-day use; only use the Computer Administrator username for software installation and configuration changes.
- Never surf the Internet with an account that has administrative privilege
- If this is a common PC for a business, ensure employees accounts are individually assigned (if practical). Ensure those employee accounts are not administrators (unless there is a need and a high degree of trust)
- Run a good commercial anti-virus program with annual software support (or a subscription)
- There are some good free AV packages (AVG, Clamwin, Avast) .. Google them for the links
- Sophos makes a good Mac AV package .. yes, Macs are vulnerable to malware as well; it’s just not as prevalent
- Finally ensure regular (daily) backups are being run to protect your business, financial, customer information from loss if there is a problem with the PC
- For setup of your wireless access point (if you have one .. sometimes it’s built into the router/firewall)
- Chose wireless encryption of at least WPA or WPA2 .. never use WEP or no encryption
- There is no significant increase in security by obscuring your network name (SSID)
- Don’t use any personally identifiable information in your network name
If you are unsure of how to do any of these steps, get one of your computer knowledgeable friends to help you. Of course if you are purchasing a new system right now, I’d strongly recommend you check out Apple’s Mac products. They’re not immune to malware, but the architecture and core are by design much less vulnerable to the types of malware that plague Windows.
Windows/AD Notes
Find all the AD groups a particular user belongs to:
dsquery user -samid username | dsget user -memberof
Find all members of an AD group:
dsquery group -samid groupname | dsget group -members
Find all inactive users:
dsquery user -disabled -inactive 12
Windows SMB/CIFS shares
Map CIFS shares:
NET USE \\1.2.3.4 /USER:DOMAIN\USERID
NET USE
NET USE \\1.2.3.4 /DELETE
Alter boot time settings:
MSCONFIG
smbclient syntax:
# mount -t smbfs -o username=user,password=pass //server/sharepoint /mnt/localmntpoint
Escape admin shares:
//wfsnt55/c\$
Reducing malware risk by removing local Administrator privileges
Running day-to-day with a Windows account that has Administrator privileges is a recipe for disaster. Casual browsing of a website that is infected or inadvertent opening of infected attachments can result in an infection through the user’s Administrator privileges. Something like 92% of Microsoft critical vulnerabilities announced in 2008 could have been mitigated by operating day-to-day as a normal user. Splitting your accounts into a normal account and admin account is a good idea, but it can lead to some headaches when the normal user needs to run temporarily as Administrator.
Fortunately there are some work arounds that can be used to temporarily elevate the user’s privileges to Administrator. Most of these involve the RUNAS command:
File explorer
If you’re running IE7 under WinXP, in order to run Windows Explorer with the runas command, it must be run as a separate process. A quick way to do this, without having to change your Folder Options settings, would be to run an instance of Explorer with the undocumented parameter /separate, like this:
runas /user:domain\username "explorer /separate"
Command Line Prompt
You can add a shortcut on the task bar with the following syntax to get an Administrator cmd prompt:
%windir%\system32\runas.exe /user:yourdomain\a-someuser cmd
yourdomain is the name of your AD domain if you have one, if not, leave it out. a-someuser is a suggested naming convention for the Administrator account associated with the user named someuser.
